Aad Application Proxy Connector Uninstall the Connector and Install It Again
Welcome to this web log post on Azure Active Directory Application Proxy. This post comes off the back of an awesome day at the Due east of England Microsoft User Group #EEMUG. In this mail nosotros will take you through the fundamentals and the requirements of Azure AD Application Proxy and how to publish your internal Web Apps to Internet connected users.
This post will focus on:-
- What is Azure Advertising Application Proxy?
- Components of Azure AD Application Proxy
- How does Azure Advertising Awarding Proxy Work?
- Awarding Proxy Connectors and Connector Groups
- Prerequisites for Azure Advertizing Application Proxy
- Installing Azure AD Application Proxy
- Creating Enterprise Apps for Azure AD Application Proxy
1 . What is Azure Ad Awarding Proxy?
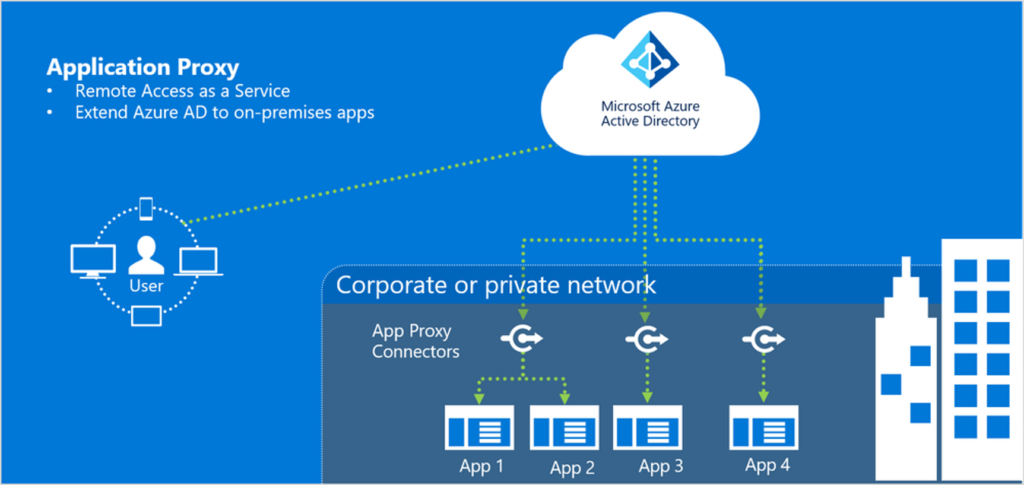
Azure Active Directory (AAD) Awarding Proxy is a characteristic of Azure Active Directory.
Information technology provides secure remote access to on-premises spider web applications such equally:-
- Web applications hosted behind a Remote Desktop Gateway
- SharePoint
- Web APIs that you want to betrayal to rich applications on unlike devices
- Rich client apps that are integrated with the Active Directory Authentication Library (ADAL)
AAD Awarding Proxy is secure. You practice not demand to open incoming ports on your firewall for internet continued users to access your internal web apps. The application proxy connector (more than on this later) only requires outbound ports fourscore & 443 to the internet.
We would typically deploy the AAD Application Proxy Service when we accept intranet sites that are not cloud ready.
two . Components of Azure AD Application Proxy
The AAD Application Proxy consists of 3 main components:-
- Azure Active Directory
- Application Proxy Service – Characteristic of AAD
- Application Proxy Connector – Installed on your intranet server(due south)
3 . How does Azure Advert Application Proxy Work?
The AAD Application Proxy can be used to pre-authenticate your users before they admission spider web apps on your intranet. In my opinion, this has to be one of its biggest advantages. If nosotros utilise AAD to pre-cosign our users, we can leverage features like Provisional Admission, MFA and other Identity Protection services.
High Level flow of the Azure Advert Application Proxy feature
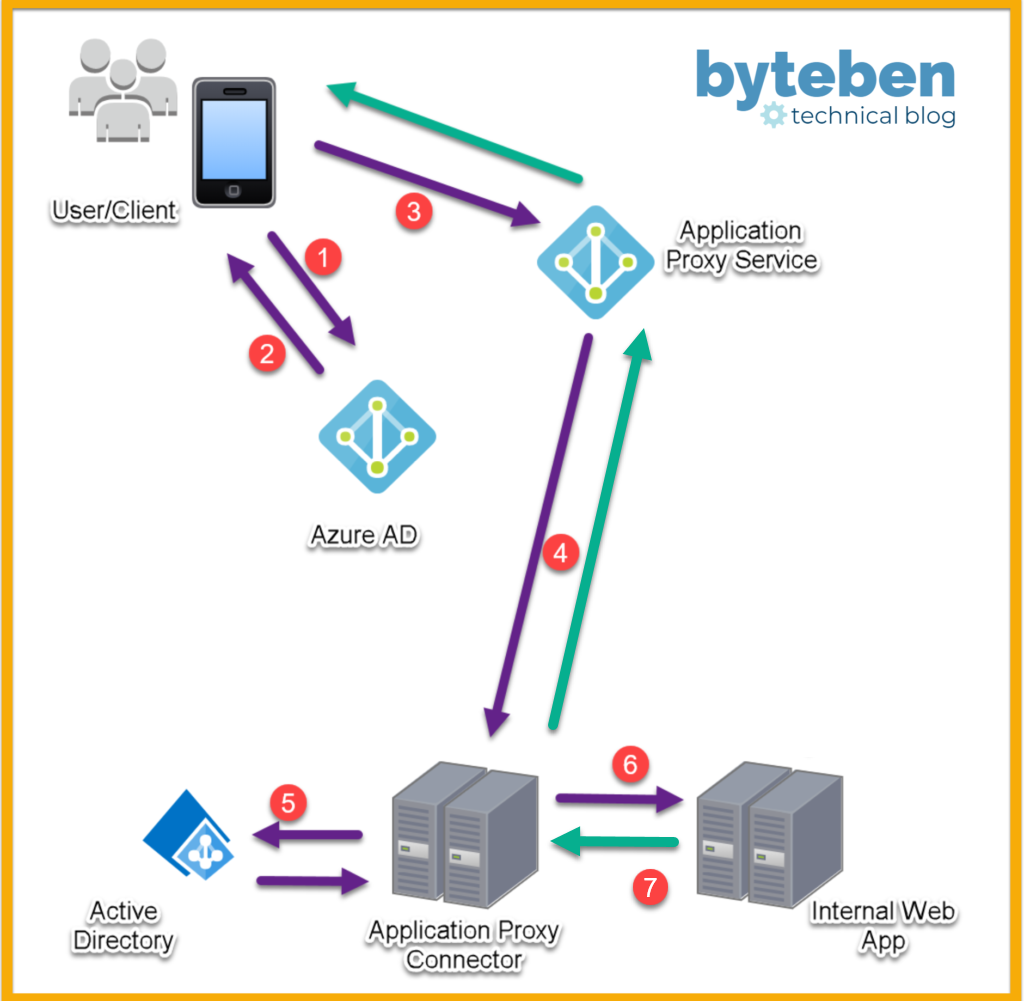
- The user access the published web app and is redirected to authenticate with Azure Advertising
- If sign-in is successful, Azure AD gives the client a token
- The client sends the token to the Application Proxy Connector Service* where the UPN and, if required, the SPN is extracted
- The request is sent to the Application Proxy Connector
- If configured for SSO, the Application Proxy Connector performs boosted hallmark (KCD) on behalf of the user
- The request is sent to the spider web app
- The spider web app responds, via the Application Proxy Service, to the user
* Call back only outbound ports are required from the Application Proxy Connector(due south). The Application Proxy Connector periodically polls the Application Proxy Service for any incoming requests
four . Application Proxy Connectors and Connector Groups
An Application Proxy Connector is downloaded and installed on a server that is preferably in the same network segment equally the back-cease web application servers.
Microsoft recommends a minimum of 2 connectors to allow for loftier availability to your back-end web awarding. They tin can exist installed manually or scripted with PowerShell (requires the utilise of offline tokens for initial service authentication). Certificates to cosign with the Connector Service are created during the initial registration and are automatically renewed by the Connectors every couple of months.
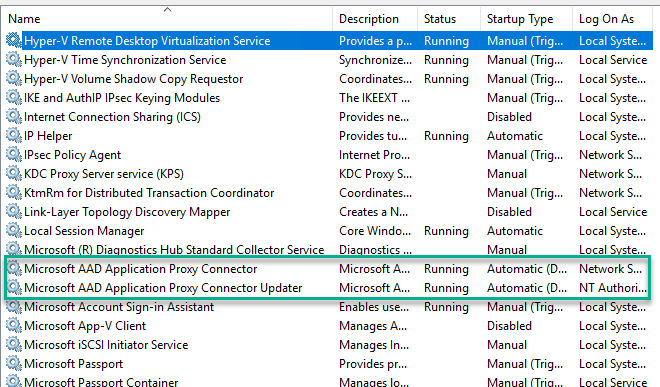
There are two services installed with each Application Proxy Connector
- Microsoft AAD Application Proxy Connector
- Microsoft AAD Application Proxy Connector Updater
The Connectors handle high availability during periods of high load or Connector unavailability.
Although not strictly necessary, solutions like Express Route should be considered to ensure Connectors can communicate quickly with the Application Proxy Service.
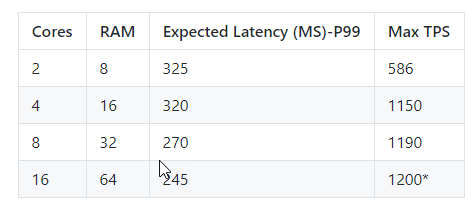
The table beneath offers an indication of how many Connectors are recommended depending on the expected number of transactions per second to your dorsum-end web awarding
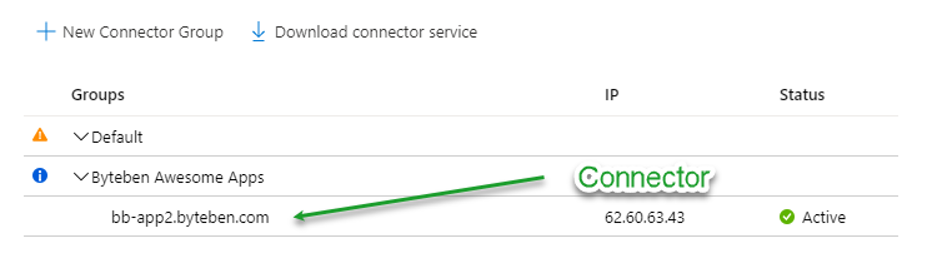
Connector Groups enable you lot to assign specific connectors to serve specific applications. Yous can grouping a number of connectors together, and so assign each awarding to a Connector Grouping.
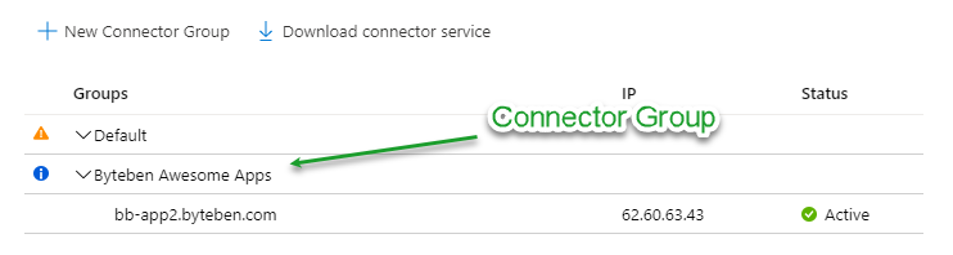
Connector groups make it easier to manage large deployments. They too amend latency for tenants that have applications hosted in different regions, considering you can create location-based connector groups to serve just local applications.
5 . Prerequisites for Azure Advertizing Awarding Proxy
You guessed it…licenses 🙂 Let'southward have a await at the pre-requisites to get up and running with the AAD Application Proxy Feature
- Users require an AAD Premium Licence (P1 or P2)
- Azure AD Tenant (Assumed)
- Application Proxy Connector machines must exist enabled for TLS 1.2
- Connectors must be installed on Server 2012R2 or higher
- Connectors must be installed on a Domain Joined machine if y'all desire single sign-on (SSO) to applications that utilize Integrated Windows Authentication (IWA) *
- It is recommended to configure a minimum of ii Proxy Connectors
- The "Awarding Administrator" or "Global Administrator" Function is required to install the connector
* Connector machines must be Domain Joined in society to perform Kerberos Constrained Delegation (KCD), on behalf of users, to the back-end web apps.
half-dozen . Installing Azure Advertising Application Proxy
7 . Creating Enterprise Apps for Azure AD Application Proxy
Summary
In this blog postal service nosotros looked at the Azure Active Directory Application Proxy. This is a really neat feature of Azure AD to let your internet based users to access internal web apps that are non ready to movement to the cloud.
Having Azure AD being able to pre-authenticate admission to these internal web apps is the big win here. This coupled with the Proxy Connector reckoner being able to perform Kerberos Constrained Delegation for a SSO experience on IWA web apps adds the icing on the cake.
If you lot would like me to expand on any area, delight annotate below. If you lot prefer step-by-footstep instructions instead of YouTube lab videos I would love to hear this feedback as well.
Thanks for reading!
Source: https://byteben.com/bb/azure-ad-application-proxy-accessing-your-internal-web-apps-from-the-internet/
0 Response to "Aad Application Proxy Connector Uninstall the Connector and Install It Again"
Post a Comment